Multicast – Static Mroute
在下面的Topology中,RP是3.3.3.3,Source和PC都是用loopback来模拟,默认组播流会经过R5到达R4并推到PC1上。由于某些原因,关掉了R5,让组播流从R1下去,发现R1有问题。为了找到原因,需要保持这个故障,但又不影响现有的组播业务,所以新增了一个Source2和PC2来做测试,在这里不用关心R1具体是什么问题,这篇总结主要是利用这个topology来展示Static Mroute的用法。
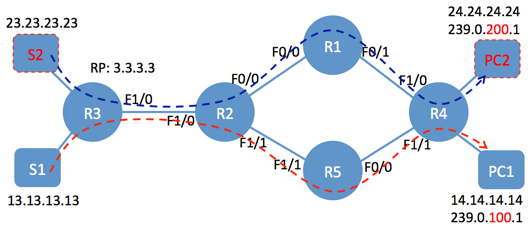
默认情况下,如果不变更配置,所有组播流都会通过R5推下去,虽然对于R4来说,R1和R5是负载的,但那仅是在IPv4的情况下,你可以看下RPF信息,就知道了,他只会选择IP地址大的,此行为描述在RFC2362,组播的负载分担不在这篇总结中讨论。
R4#sh ip route 3.3.3.3 Routing entry for 3.3.3.3/32 Known via "isis", distance 115, metric 30, type level-2 Redistributing via isis Last update from 14.1.1.1 on FastEthernet1/0, 1d02h ago Routing Descriptor Blocks: * 45.1.1.5, from 3.3.3.3, via FastEthernet1/1 Route metric is 30, traffic share count is 1 14.1.1.1, from 3.3.3.3, via FastEthernet1/0 Route metric is 30, traffic share count is 1 R4#sh ip rpf 3.3.3.3 RPF information for ? (3.3.3.3) RPF interface: FastEthernet1/1 RPF neighbor: ? (45.1.1.5) RPF route/mask: 3.3.3.3/32 RPF type: unicast (isis) RPF recursion count: 0 Doing distance-preferred lookups across tables
所以这种情况下就需要用到Static Mroute,命令非常简单,如下所示:
R4(config)#ip mroute 23.23.23.23 255.255.255.255 14.1.1.1
静态组播主要修改Source的RPF路径,PC发送的组join报文是根据RPF(反向路径检测)的信息去找RP注册的。对于R4来说,这里有两个RPF neighbor,R1和R5。如上说述,默认只会选择地址最大的R5,所以在配置RPF neighbor时,指向R4,也就是14.1.1.1,只有Source为23.23.23.23受到此组播路由的影响,下面看看变化:
加Static Mroute前,看下现有R3的组播表项:
R3#sh ip mroute
IP Multicast Routing Table
Flags: D - Dense, S - Sparse, B - Bidir Group, s - SSM Group, C - Connected,
L - Local, P - Pruned, R - RP-bit set, F - Register flag,
T - SPT-bit set, J - Join SPT, M - MSDP created entry,
X - Proxy Join Timer Running, A - Candidate for MSDP Advertisement,
U - URD, I - Received Source Specific Host Report,
Z - Multicast Tunnel, z - MDT-data group sender,
Y - Joined MDT-data group, y - Sending to MDT-data group,
V - RD & Vector, v - Vector
Outgoing interface flags: H - Hardware switched, A - Assert winner
Timers: Uptime/Expires
Interface state: Interface, Next-Hop or VCD, State/Mode
(*, 239.0.100.1), 00:04:18/00:03:06, RP 3.3.3.3, flags: S
Incoming interface: Null, RPF nbr 0.0.0.0
Outgoing interface list:
FastEthernet1/0, Forward/Sparse, 00:04:18/00:03:06
(*, 224.0.1.40), 00:04:33/00:02:51, RP 3.3.3.3, flags: SJCL
Incoming interface: Null, RPF nbr 0.0.0.0
Outgoing interface list:
FastEthernet1/0, Forward/Sparse, 00:04:33/00:02:51
对于R3来说,只有PC1的组注册信息;incoming是null,说明Source还没注册。这个信息跟R5和R2的输出类似,而对于R1来说,是没有该组的注册信息,如上所述,注册信息只会根据RPF的结果传送。另外224.0.1.40是RP发现协议的组地址。下面是在R4上添加一个新组239.0.200.1后,R1和R5的信息:
R4#sh run int lo2 Building configuration... Current configuration : 119 bytes ! interface Loopback2 ip address 24.24.24.24 255.255.255.255 ip pim sparse-mode ip igmp join-group 239.0.200.1 end R1#sh ip mroute IP Multicast Routing Table Outgoing interface flags: H - Hardware switched, A - Assert winner Timers: Uptime/Expires Interface state: Interface, Next-Hop or VCD, State/Mode (*, 224.0.1.40), 1d16h/00:02:13, RP 3.3.3.3, flags: SJPL Incoming interface: FastEthernet0/0, RPF nbr 12.1.1.2 Outgoing interface list: Null R5#sh ip mroute IP Multicast Routing Table Outgoing interface flags: H - Hardware switched, A - Assert winner Timers: Uptime/Expires Interface state: Interface, Next-Hop or VCD, State/Mode (*, 239.0.100.1), 01:11:33/00:03:14, RP 3.3.3.3, flags: S Incoming interface: FastEthernet1/1, RPF nbr 25.1.1.2 Outgoing interface list: FastEthernet0/0, Forward/Sparse, 01:11:33/00:03:14 (*, 239.0.200.1), 00:02:34/00:02:54, RP 3.3.3.3, flags: S Incoming interface: FastEthernet1/1, RPF nbr 25.1.1.2 Outgoing interface list: FastEthernet0/0, Forward/Sparse, 00:02:34/00:02:54 (*, 224.0.1.40), 01:12:21/00:02:56, RP 3.3.3.3, flags: SJCL Incoming interface: FastEthernet1/1, RPF nbr 25.1.1.2 Outgoing interface list: FastEthernet0/0, Forward/Sparse, 01:12:21/00:03:18
在R3上用Ping来触发Source注册:
R3#ping 239.0.200.1 source lo2
Type escape sequence to abort.
Sending 1, 100-byte ICMP Echos to 239.0.200.1, timeout is 2 seconds:
Packet sent with a source address of 23.23.23.23
Reply to request 0 from 45.1.1.4, 12 ms
Reply to request 0 from 45.1.1.4, 20 ms
R3#ping 239.0.100.1 source lo1
Type escape sequence to abort.
Sending 1, 100-byte ICMP Echos to 239.0.100.1, timeout is 2 seconds:
Packet sent with a source address of 13.13.13.13
Reply to request 0 from 45.1.1.4, 12 ms
Reply to request 0 from 45.1.1.4, 16 ms
R3#
R3#sh ip mroute
IP Multicast Routing Table
Outgoing interface flags: H - Hardware switched, A - Assert winner
Timers: Uptime/Expires
Interface state: Interface, Next-Hop or VCD, State/Mode
(*, 239.0.100.1), 04:45:58/stopped, RP 3.3.3.3, flags: S
Incoming interface: Null, RPF nbr 0.0.0.0
Outgoing interface list:
FastEthernet1/0, Forward/Sparse, 04:45:58/00:02:47
(13.13.13.13, 239.0.100.1), 00:00:23/00:02:38, flags: JT
Incoming interface: Loopback1, RPF nbr 0.0.0.0
Outgoing interface list:
FastEthernet1/0, Forward/Sparse, 00:00:23/00:02:36, A
(*, 239.0.200.1), 03:37:58/stopped, RP 3.3.3.3, flags: S
Incoming interface: Null, RPF nbr 0.0.0.0
Outgoing interface list:
FastEthernet1/0, Forward/Sparse, 03:37:58/00:02:35
(23.23.23.23, 239.0.200.1), 00:00:46/00:02:20, flags: JT
Incoming interface: Loopback2, RPF nbr 0.0.0.0
Outgoing interface list:
FastEthernet1/0, Forward/Sparse, 00:00:46/00:02:13, A
(*, 224.0.1.40), 04:46:13/00:02:37, RP 3.3.3.3, flags: SJCL
Incoming interface: Null, RPF nbr 0.0.0.0
Outgoing interface list:
FastEthernet1/0, Forward/Sparse, 04:46:13/00:02:37
在R4上实施Static Mroute,看结果,注意静态组播只改变了(S,G)的信息,对于(*,G)无法改变,所以你会看到下面(*,G)没有变,仍然是从R5走
R4#config ter
Enter configuration commands, one per line. End with CNTL/Z.
R4(config)#ip mroute 23.23.23.23 255.255.255.255 14.1.1.1
R4(config)#end
R4#
R4#sh ip mroute
IP Multicast Routing Table
Outgoing interface flags: H - Hardware switched, A - Assert winner
Timers: Uptime/Expires
Interface state: Interface, Next-Hop or VCD, State/Mode
(*, 239.0.100.1), 01:56:42/stopped, RP 3.3.3.3, flags: SJCL
Incoming interface: FastEthernet1/1, RPF nbr 45.1.1.5
Outgoing interface list:
Loopback1, Forward/Sparse, 01:56:42/00:02:10
(13.13.13.13, 239.0.100.1), 00:01:00/00:02:03, flags: LJT
Incoming interface: FastEthernet1/1, RPF nbr 45.1.1.5
Outgoing interface list:
Loopback1, Forward/Sparse, 00:01:00/00:02:10
(*, 239.0.200.1), 01:54:07/00:02:23, RP 3.3.3.3, flags: SJCL
Incoming interface: FastEthernet1/1, RPF nbr 45.1.1.5
Outgoing interface list:
Loopback2, Forward/Sparse, 01:54:07/00:02:18
(23.23.23.23, 239.0.200.1), 00:00:36/00:02:23, flags: LJ
Incoming interface: FastEthernet1/0, RPF nbr 14.1.1.1, Mroute
Outgoing interface list:
Loopback2, Forward/Sparse, 00:00:36/00:02:23
(*, 224.0.1.40), 01:56:42/00:02:32, RP 3.3.3.3, flags: SJCL
Incoming interface: FastEthernet1/1, RPF nbr 45.1.1.5
Outgoing interface list:
FastEthernet1/0, Forward/Sparse, 01:56:42/00:02:27
R4# sh ip rpf 23.23.23.23
RPF information for ? (23.23.23.23)
RPF interface: FastEthernet1/0
RPF neighbor: ? (14.1.1.1)
RPF route/mask: 23.23.23.23/32
RPF type: static
RPF recursion count: 0
Doing distance-preferred lookups across tables
R4#sh ip rpf 13.13.13.13
RPF information for ? (13.13.13.13)
RPF interface: FastEthernet1/1
RPF neighbor: ? (45.1.1.5)
RPF route/mask: 13.13.13.13/32
RPF type: unicast (isis)
RPF recursion count: 0
Doing distance-preferred lookups across tables
事实上这里就有些问题了,因为用Static Mroute只改变了(S, G)的路径而没改(*, G)的,所以会有两条注册信息,一条是经过R5的,一条是经过R1的,看上去没什么问题,但是看下R2就会发现,OIL中有两个output,分别指向了R1和R5,所以组播会发到R1和R5上,然后发现R5没有(S, G),drop组播,如果想避免R2向R5发送组播,只能通过SSM来解决了,因为SSM不会产生(*, G)
R2#sh ip mroute
IP Multicast Routing Table
Outgoing interface flags: H - Hardware switched, A - Assert winner
Timers: Uptime/Expires
Interface state: Interface, Next-Hop or VCD, State/Mode
(*, 239.0.100.1), 00:09:36/00:02:50, RP 3.3.3.3, flags: S
Incoming interface: FastEthernet1/0, RPF nbr 23.1.1.3
Outgoing interface list:
FastEthernet1/1, Forward/Sparse, 00:09:32/00:02:50
(13.13.13.13, 239.0.100.1), 00:02:48/00:02:39, flags: T
Incoming interface: FastEthernet1/0, RPF nbr 23.1.1.3
Outgoing interface list:
FastEthernet1/1, Forward/Sparse, 00:02:48/00:02:50
(*, 239.0.200.1), 00:09:38/00:03:13, RP 3.3.3.3, flags: S
Incoming interface: FastEthernet1/0, RPF nbr 23.1.1.3
Outgoing interface list:
FastEthernet1/1, Forward/Sparse, 00:09:06/00:03:13
(23.23.23.23, 239.0.200.1), 00:00:28/00:03:09, flags: T
Incoming interface: FastEthernet1/0, RPF nbr 23.1.1.3
Outgoing interface list:
FastEthernet0/0, Forward/Sparse, 00:00:28/00:03:01
FastEthernet1/1, Forward/Sparse, 00:00:29/00:03:13
(*, 224.0.1.40), 00:09:40/00:02:44, RP 3.3.3.3, flags: SJCL
Incoming interface: FastEthernet1/0, RPF nbr 23.1.1.3
Outgoing interface list:
FastEthernet1/1, Forward/Sparse, 00:09:16/00:03:06
FastEthernet0/0, Forward/Sparse, 00:09:40/00:02:25
R1#sh ip mroute
IP Multicast Routing Table
Outgoing interface flags: H - Hardware switched, A - Assert winner
Timers: Uptime/Expires
Interface state: Interface, Next-Hop or VCD, State/Mode
(*, 239.0.200.1), 00:03:13/stopped, RP 3.3.3.3, flags: SP
Incoming interface: FastEthernet0/0, RPF nbr 12.1.1.2
Outgoing interface list: Null
(23.23.23.23, 239.0.200.1), 00:03:13/00:00:17, flags:
Incoming interface: FastEthernet0/0, RPF nbr 12.1.1.2
Outgoing interface list:
FastEthernet0/1, Forward/Sparse, 00:03:13/00:03:14
(*, 224.0.1.40), 1d20h/00:02:25, RP 3.3.3.3, flags: SJPL
Incoming interface: FastEthernet0/0, RPF nbr 12.1.1.2
Outgoing interface list: Null
R5#sh ip mroute
IP Multicast Routing Table
Outgoing interface flags: H - Hardware switched, A - Assert winner
Timers: Uptime/Expires
Interface state: Interface, Next-Hop or VCD, State/Mode
(*, 239.0.100.1), 01:42:43/00:02:46, RP 3.3.3.3, flags: S
Incoming interface: FastEthernet1/1, RPF nbr 25.1.1.2
Outgoing interface list:
FastEthernet0/0, Forward/Sparse, 01:42:43/00:02:46
(13.13.13.13, 239.0.100.1), 00:02:45/00:00:44, flags:
Incoming interface: FastEthernet1/1, RPF nbr 25.1.1.2
Outgoing interface list:
FastEthernet0/0, Forward/Sparse, 00:02:45/00:02:46
(*, 239.0.200.1), 01:43:15/00:03:01, RP 3.3.3.3, flags: S
Incoming interface: FastEthernet1/1, RPF nbr 25.1.1.2
Outgoing interface list:
FastEthernet0/0, Forward/Sparse, 01:43:04/00:03:01
(*, 224.0.1.40), 01:43:24/00:02:34, RP 3.3.3.3, flags: SJCL
Incoming interface: FastEthernet1/1, RPF nbr 25.1.1.2
Outgoing interface list:
FastEthernet0/0, Forward/Sparse, 01:42:34/00:02:58
本文出自 Frank's Blog
翻译下,可以放到TZ上。
这边没放,另一篇组播的放在上面了,你可以拿“Analyzing mVPN by Wireshark”来search,我稍后把这边也上传